Implementing DevSecOps with Docker and Kubernetes: An Experiential Guide to Operate in the DevOps Environment for Securing and Monitoring Container Applications (English Edition): Ortega Candel, José Manuel: 9789355511188: Amazon.com: Books
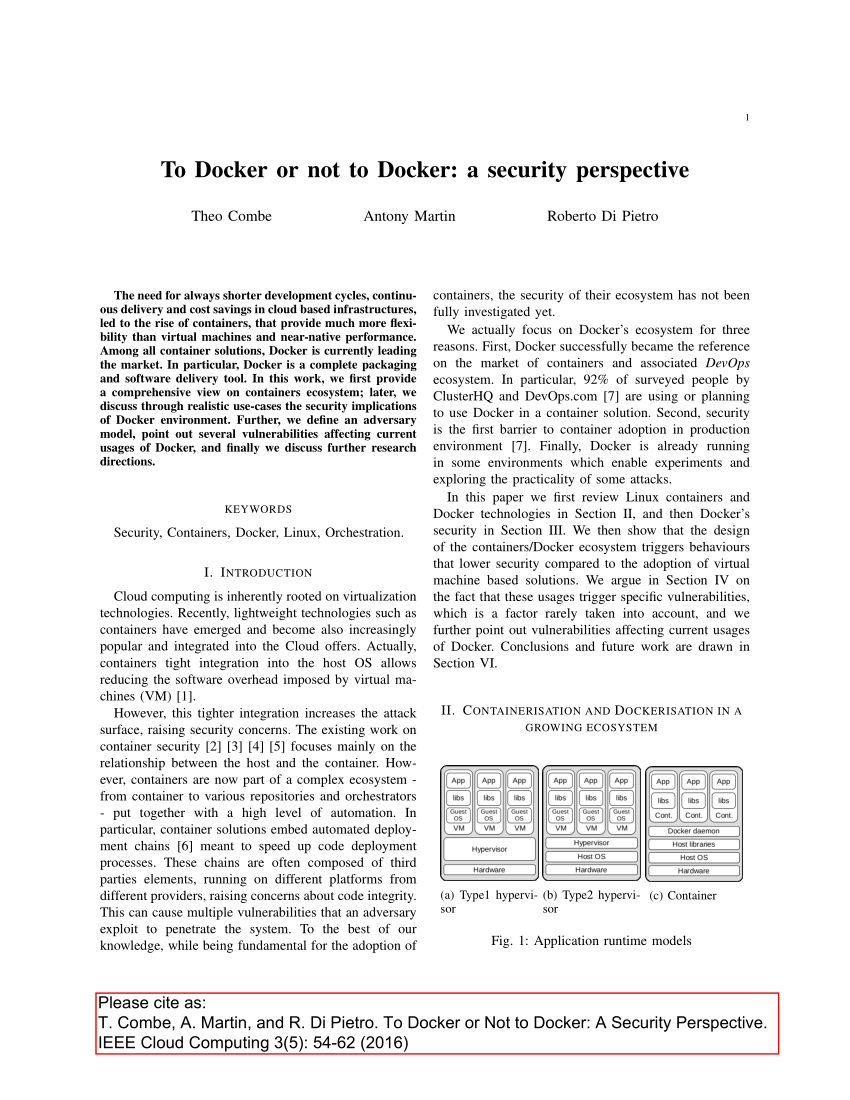
Applied Sciences | Free Full-Text | Design and Implementation of Cloud Docker Application Architecture Based on Machine Learning in Container Management for Smart Manufacturing