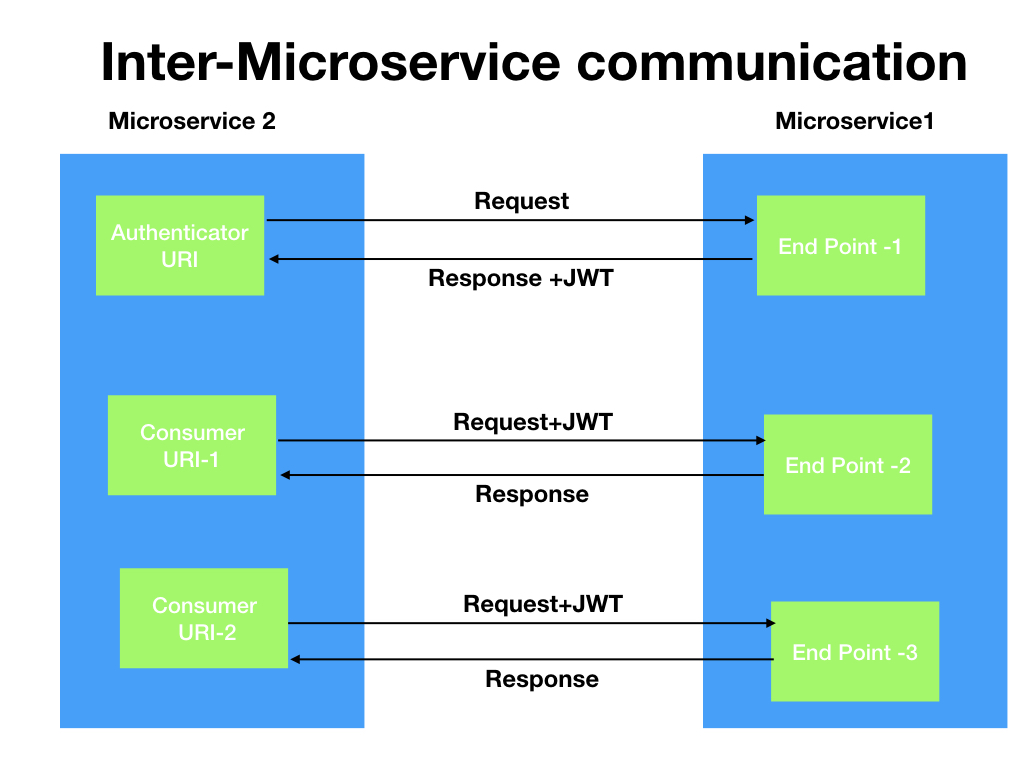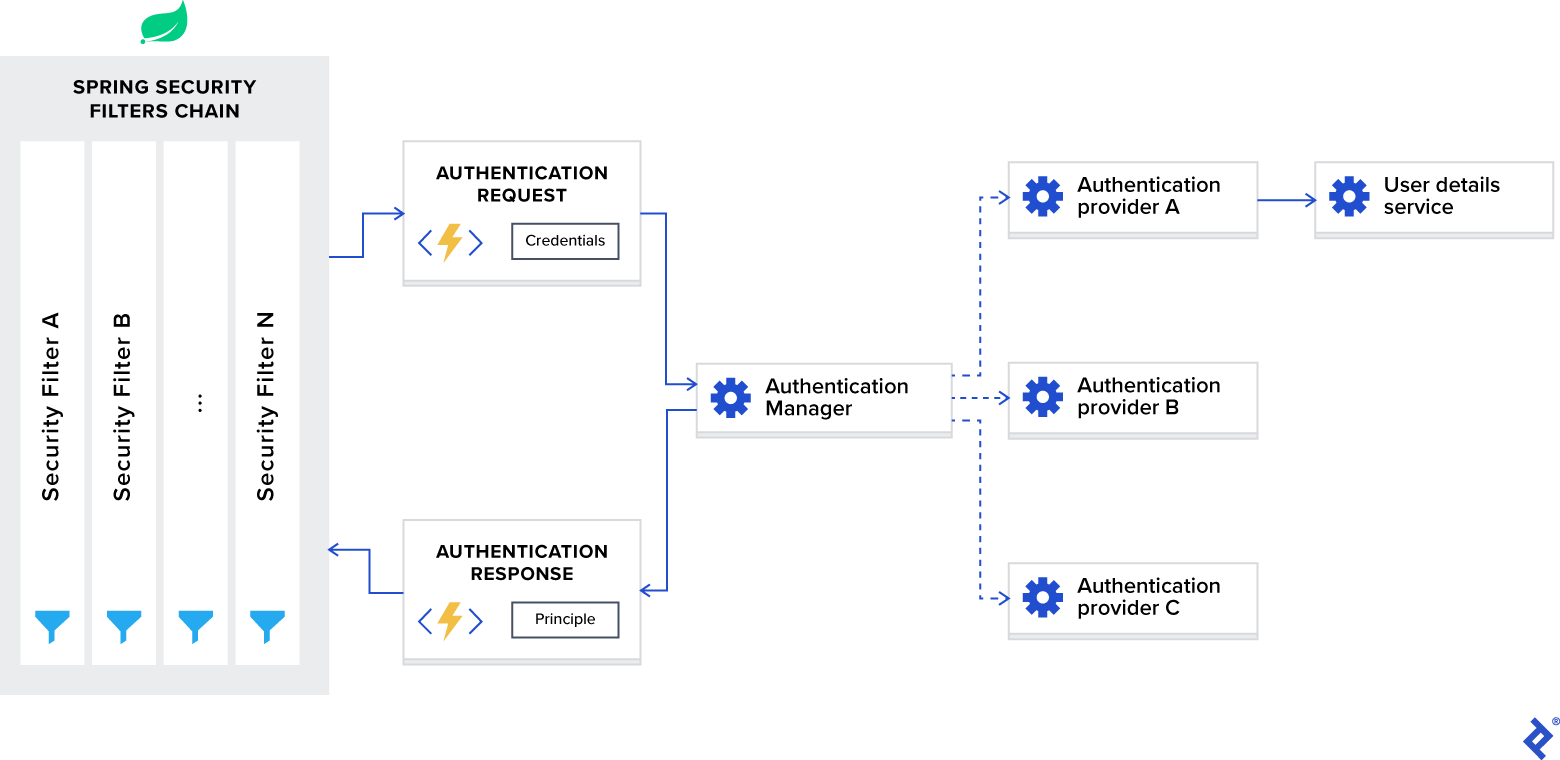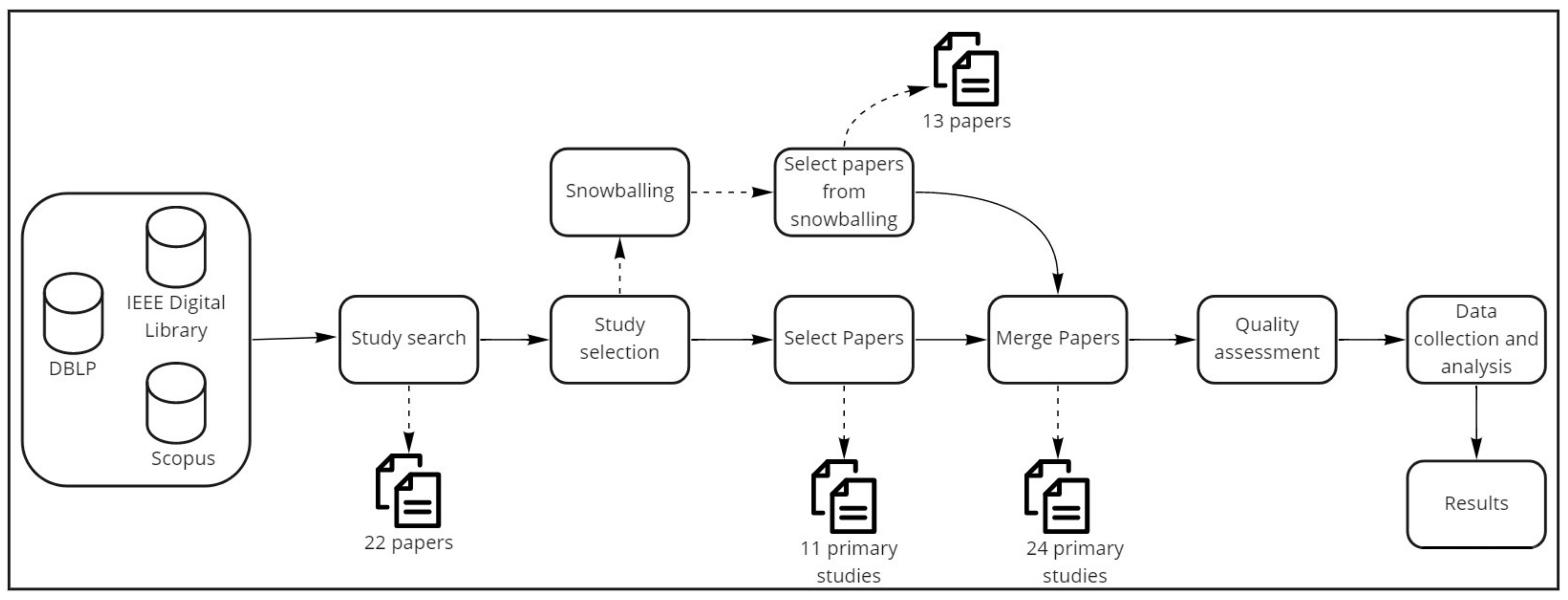
Applied Sciences | Free Full-Text | Authentication and Authorization in Microservices Architecture: A Systematic Literature Review
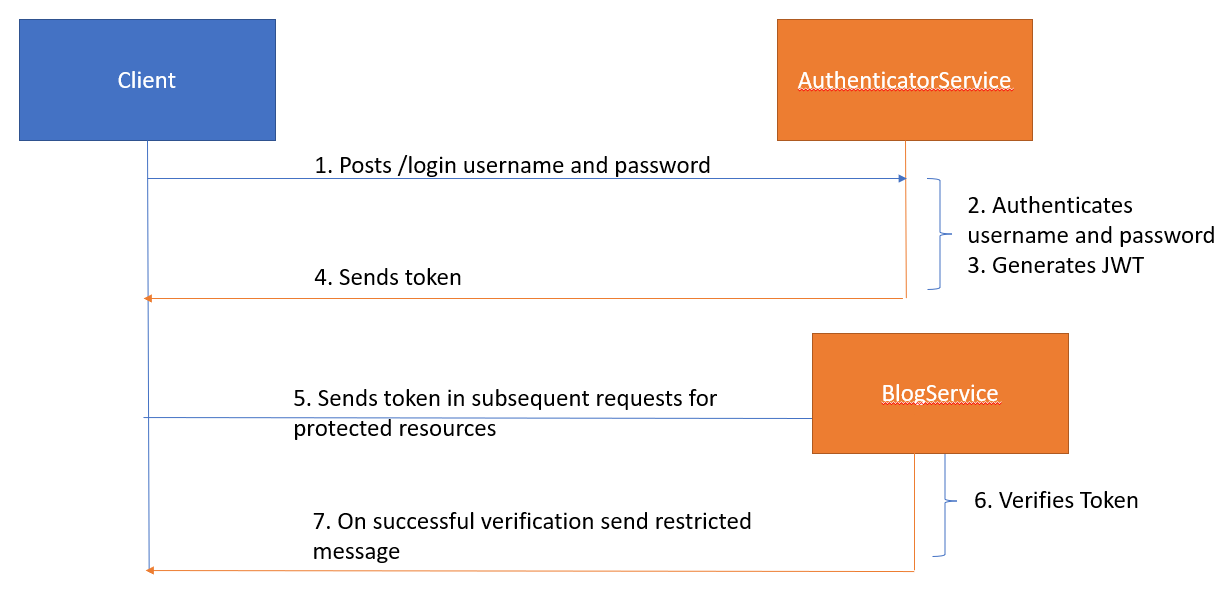
Top 10 Courses to Learn Spring Security, OAuth2, and JWT with Spring Boot for Java Developers in 2023 | by javinpaul | Javarevisited | Medium

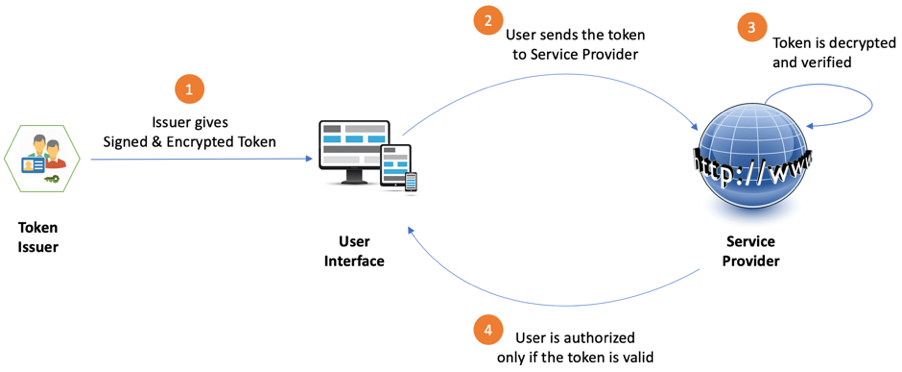
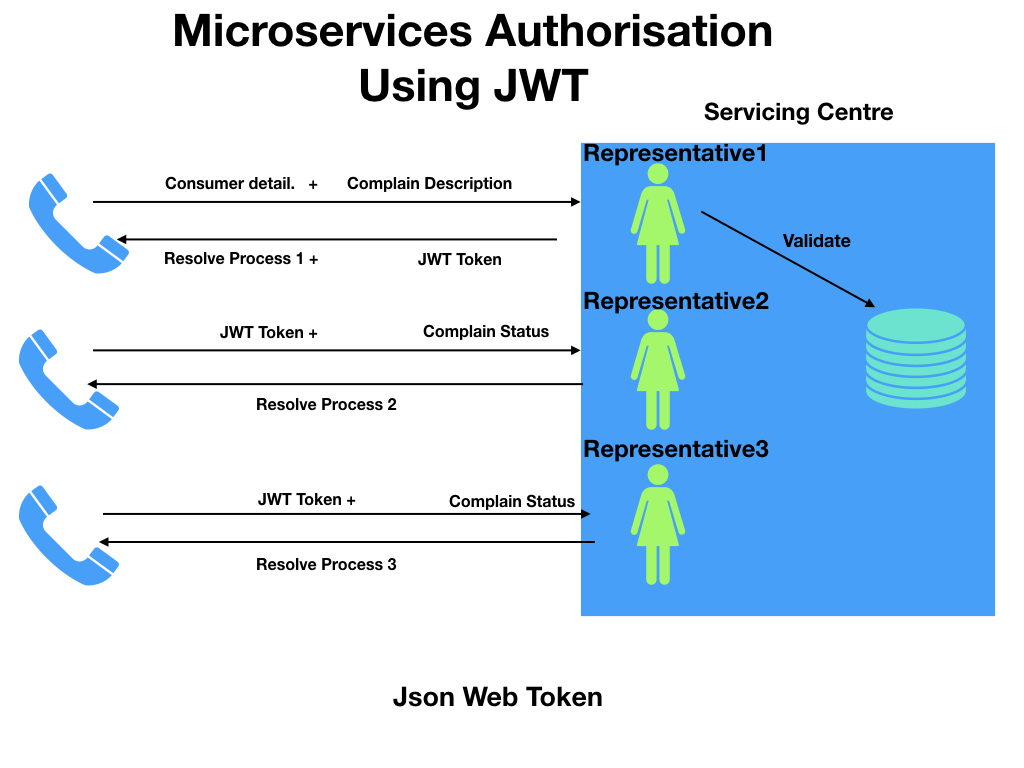
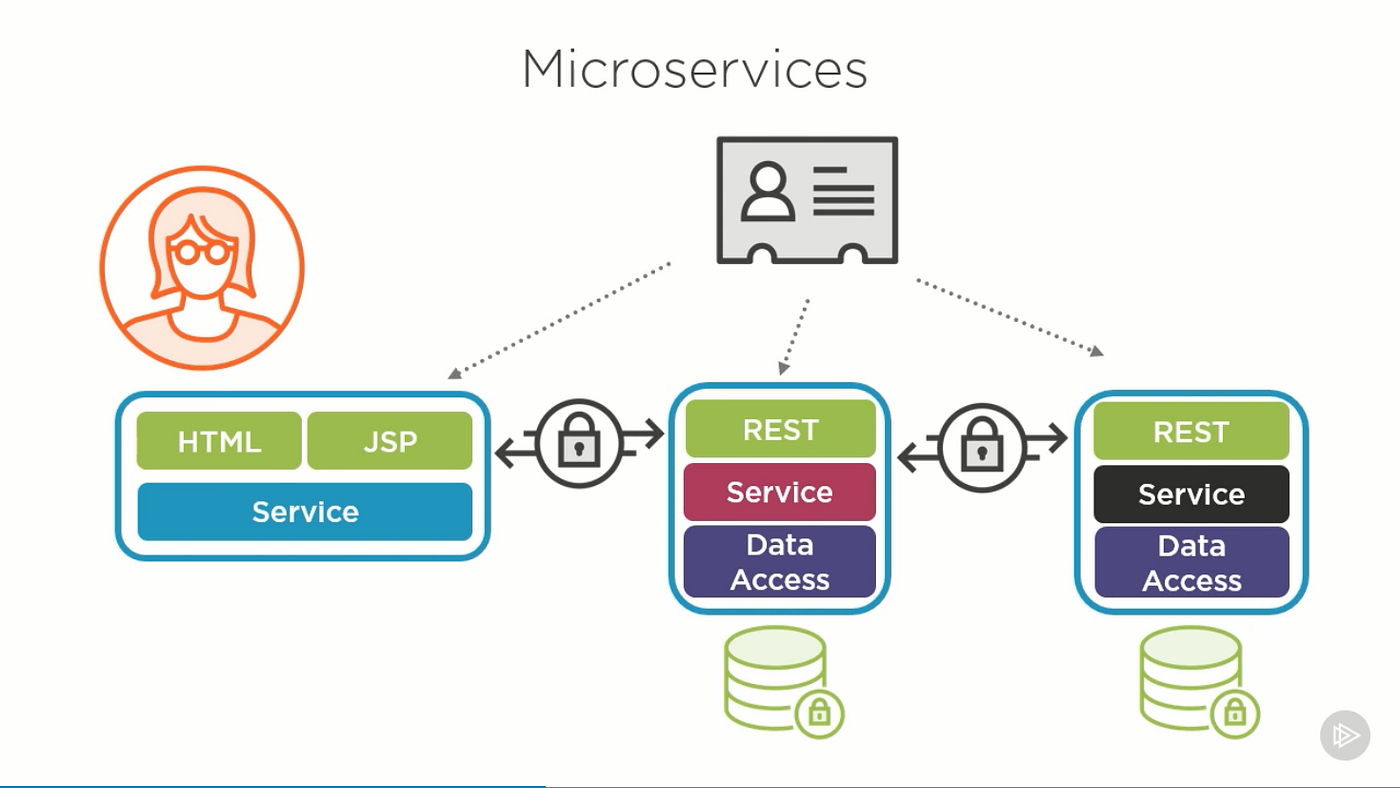
What is JWT and why do we need it in a microservices based application? - Blogs, Ideas, Train of Thoughts
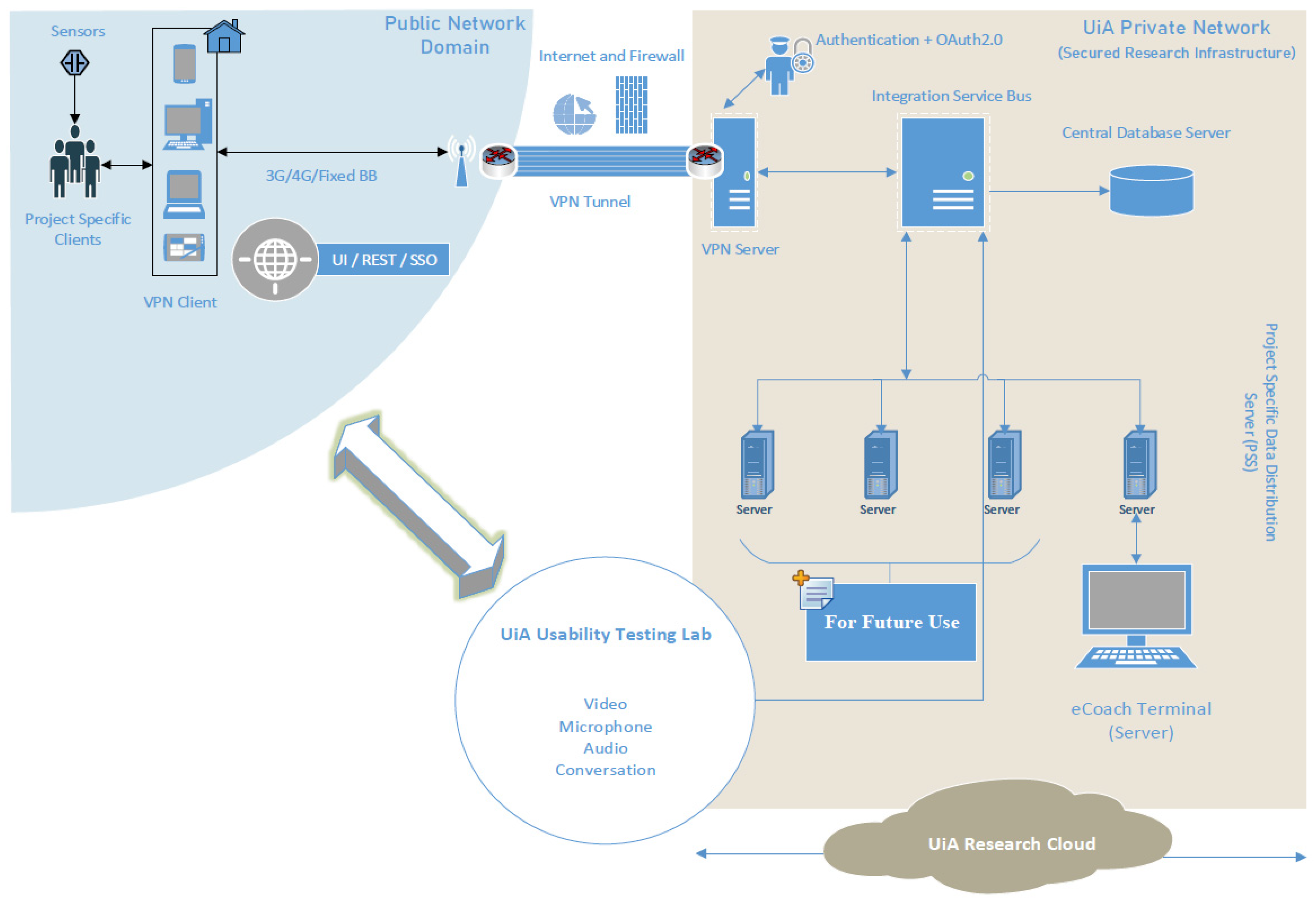
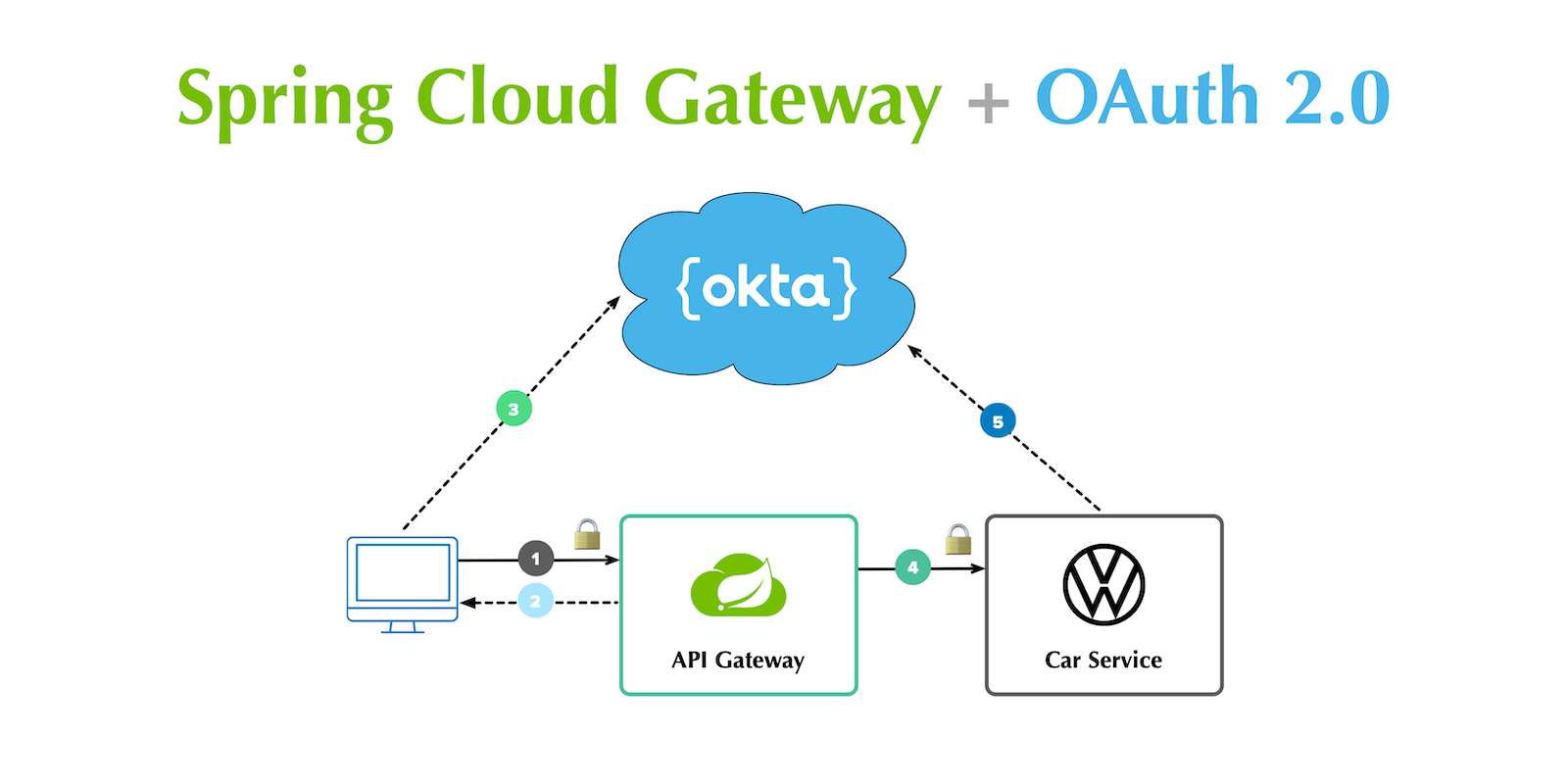
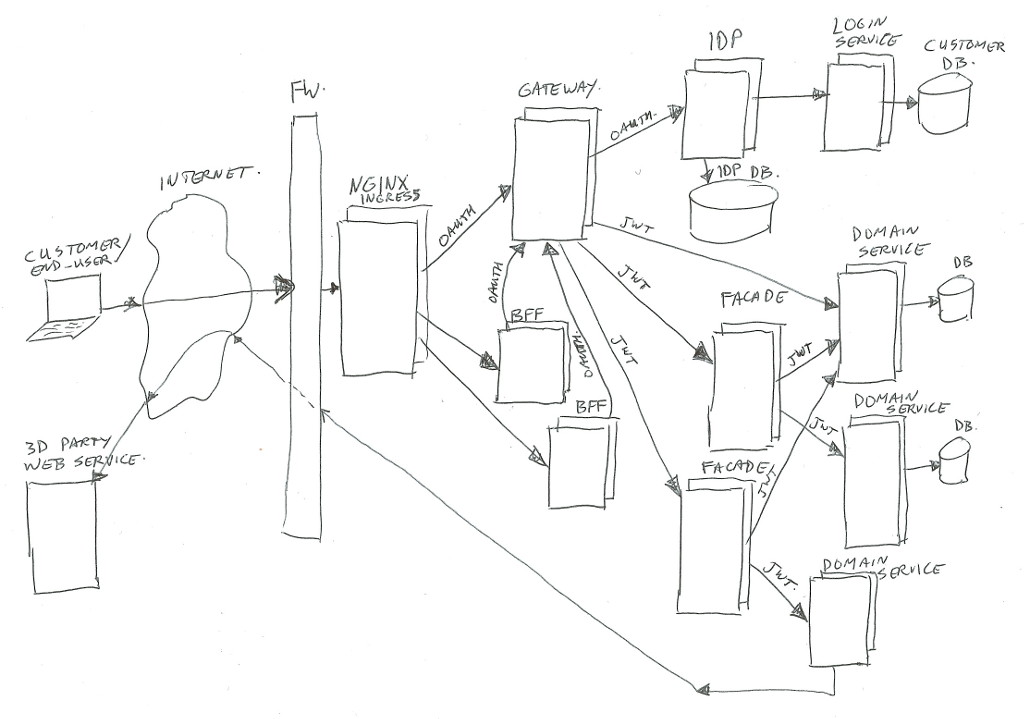
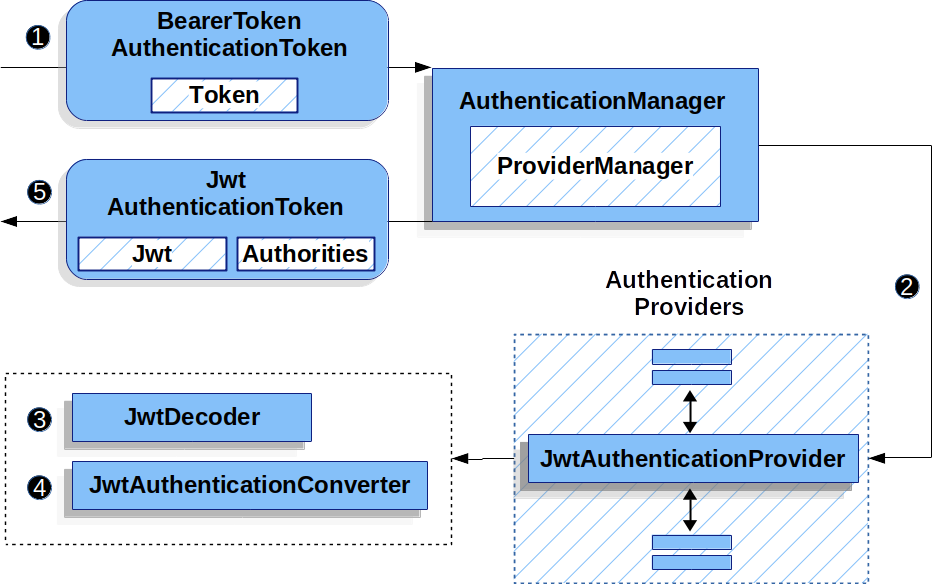
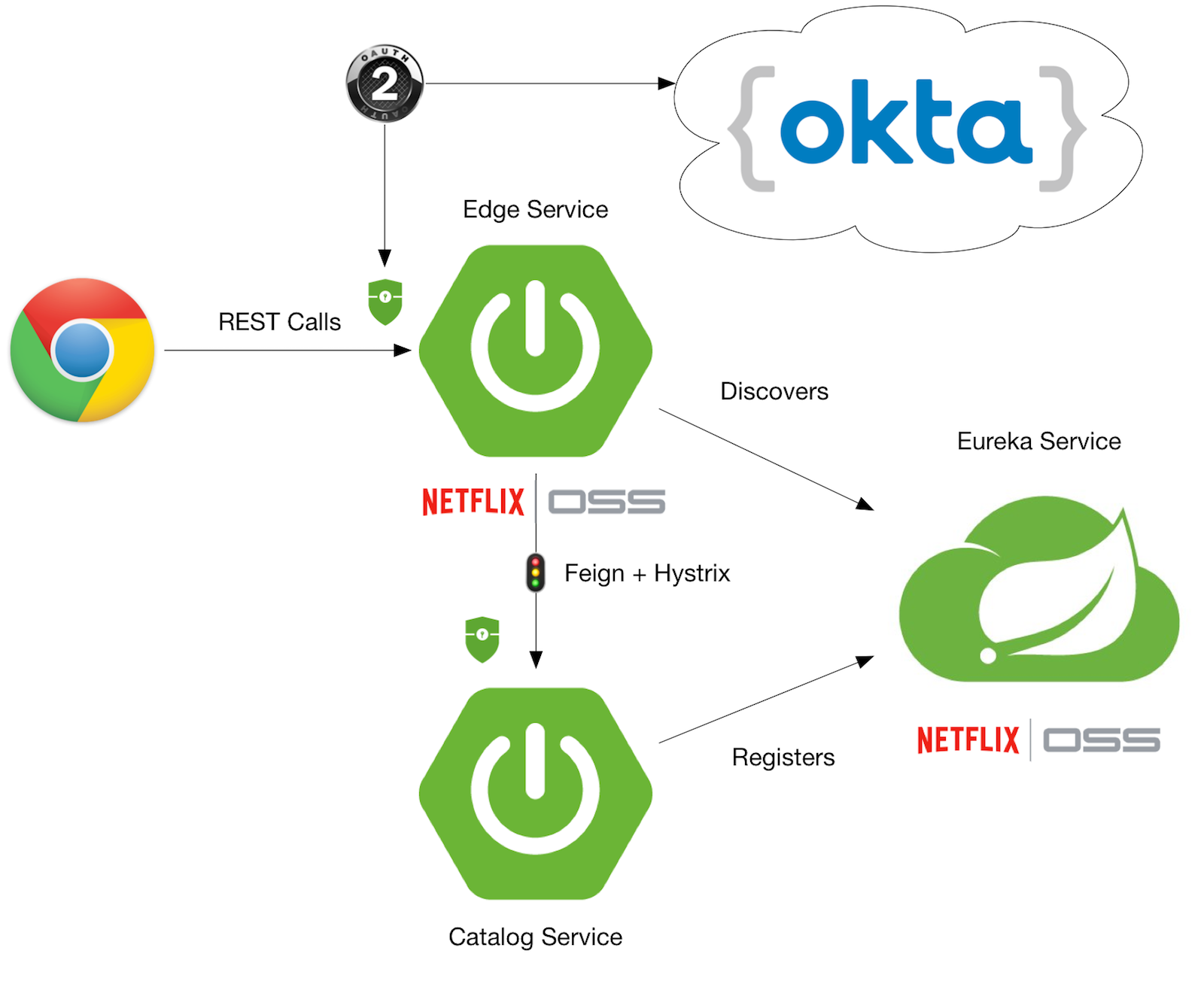
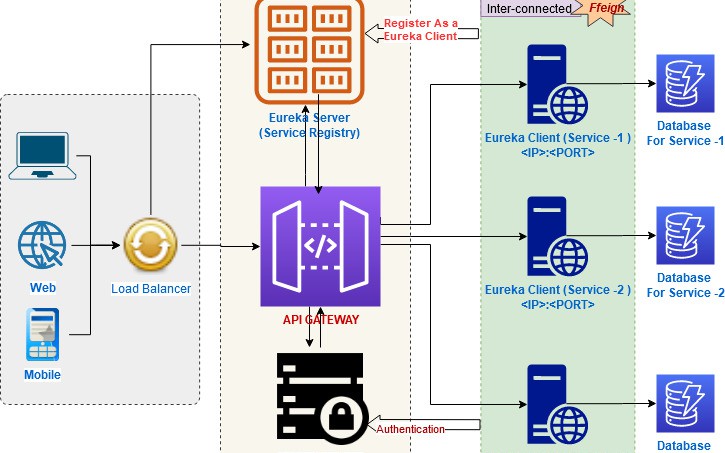
Sensors | Free Full-Text | Applying Spring Security Framework with KeyCloak-Based OAuth2 to Protect Microservice Architecture APIs: A Case Study

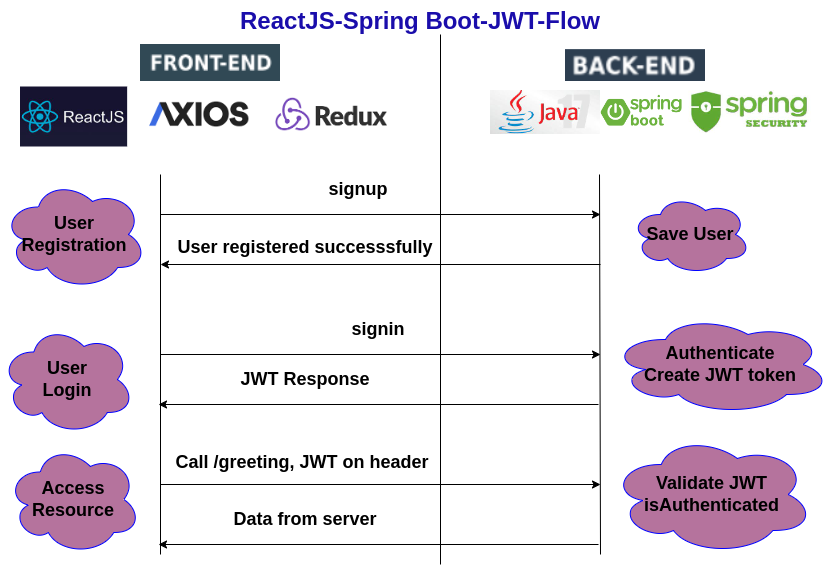
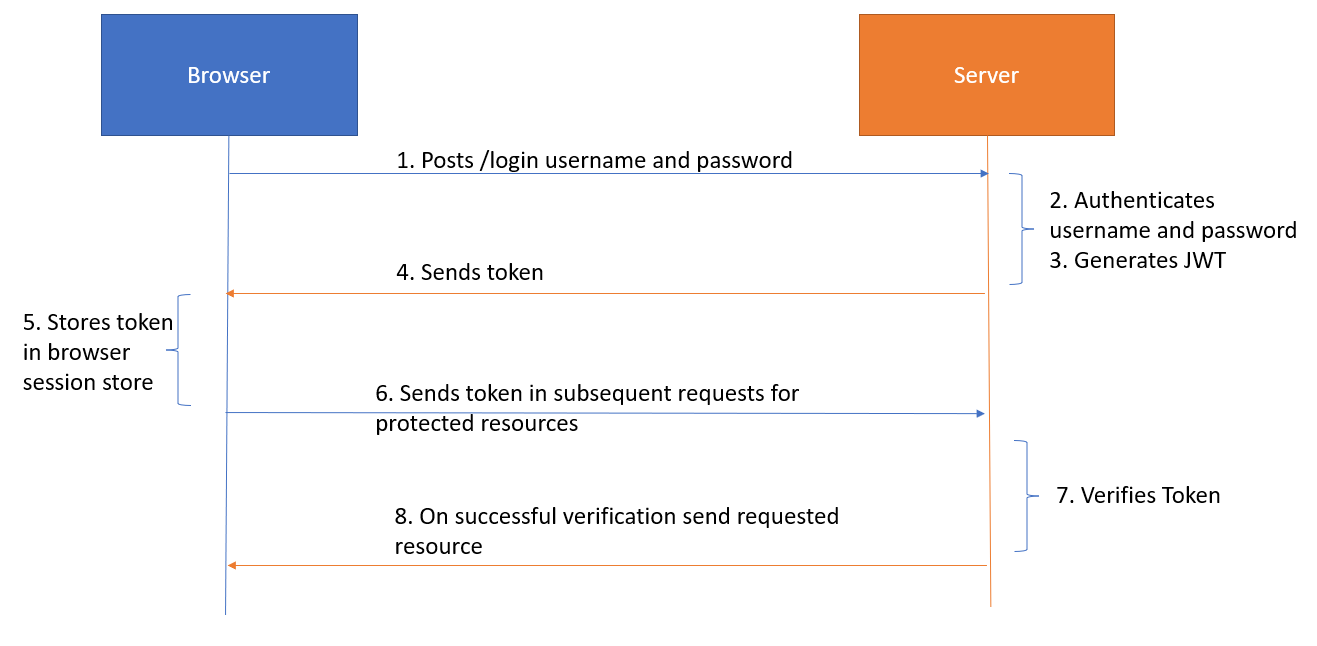
Configuring Spring Security for JWT for authorization - Extending, Securing, and Dockerizing Spring Boot Microservices Video Tutorial | LinkedIn Learning, formerly Lynda.com